Google Enhances Android 14 OS Cellular Network Security


Read in other languages:
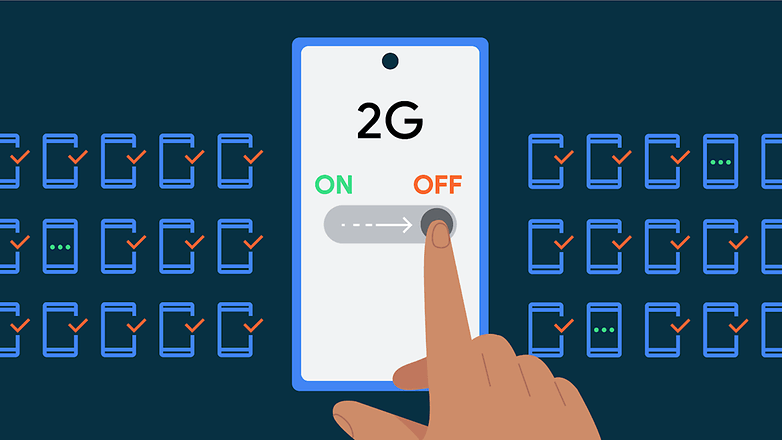
Although smartphones and tablets are mostly relying on newer cellular generations like 4G and 5G, these devices still come and support older types of networks like 2G. These obsolete technologies present underlying security threats and higher risks to be utilized in cyberattacks. In Android 14, Google is further enhancing 2G use for enterprise-level and cellular security for general users.
- Don't miss: Everything you should about Google Passkey
Disable 2G on Android 14 devices during attacks
Firstly, the upcoming major Android update will address major risks associated with a 2G network. This is specific to attackers taking advantage of the outdated security features of 2G and coming up with sophisticated ways that a target device will be downgraded to this network.
To counter this, Google will give Android Enterprise administrators the ability to design their managed hardware system to restrict it from using a 2G network in addition to doing this remotely. At the same time, supporting phone models already have a feature where a user can disable using 2G directly on the device when there is a threat.
Protection against cellular null cipher
What's available to the majority of users is improved protection from cellular null cipher connectivity. This kind of attack, like the Stingray, typically tricks the network so the connection it uses is encrypted. So instead, it allows criminals to intercept and eavesdrop the information such as SMS and voice calls that are being exchanged between a network and a device.
Google has resolved this by giving users an option to disable null cipher connections through their smartphone at the modem-level. While turned off, Google said that communication is still possible, so users can still make calls for emergency uses. This feature is planned to be added to Android 14 OS, which will start shipping to compatible devices later this year.
Apart from these two additions, what other security features do wish Google will add to the Android OS? Tell us your opinion in the comment section.
Source: Google Security Blog